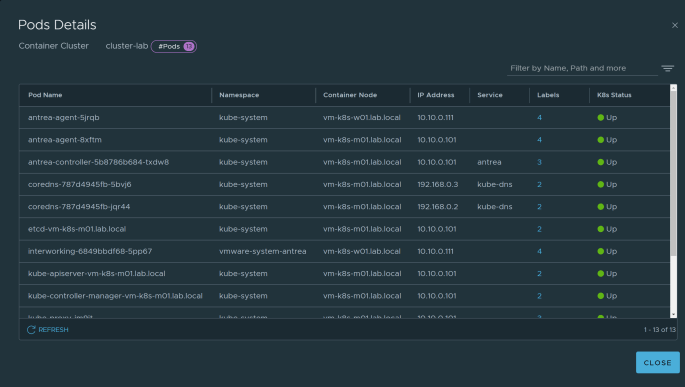
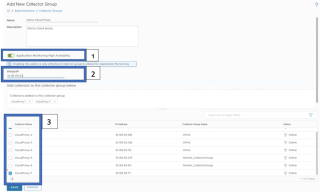
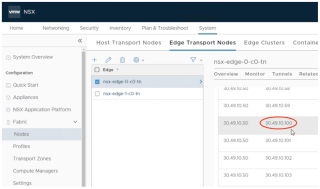
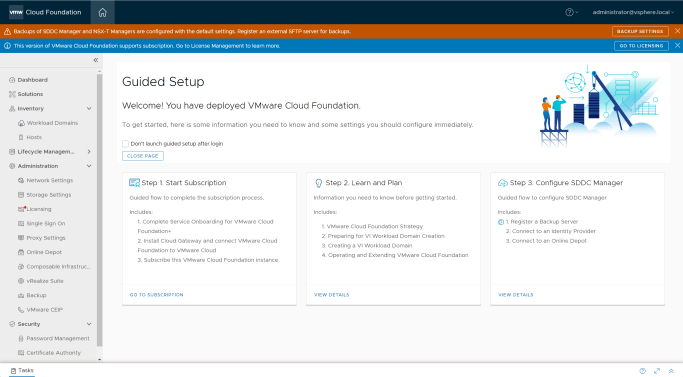
It’s been a long time since I write a blog due to different projects I am working on. One of the interesting one is how can we more secure our containerized applications. There is K8S network policies and a lot of different CNIs to achieve same but is there a way to manage security from a single UI? Can I manage security policies on different virtual machines along with K8S pods running on different platforms all from a single place? Answer is yes by harnessing the power of Antrea with NSX. VMware introduces support for Antrea integration with NSX-T 3.2 and is adding more features with different release. In this blog series, I will focus on how to build a K8S platform from scratch, Install Antrea on a vanilla K8S (no managed platform) and integrate same with NSX. Link to other part of blogs –
Securing K8S Pods using Antrea with NSX – Part 2
Later on, will see how can we utilize NSX to provide more security to our applications. So, buckle your seatbelts as we head on this roller coaster ride.
Continue reading “Securing K8S Pods using Antrea with NSX – Part 1” →